("Research"
terminated...I just don't have the time or the resources to do what I
want with this thing...)
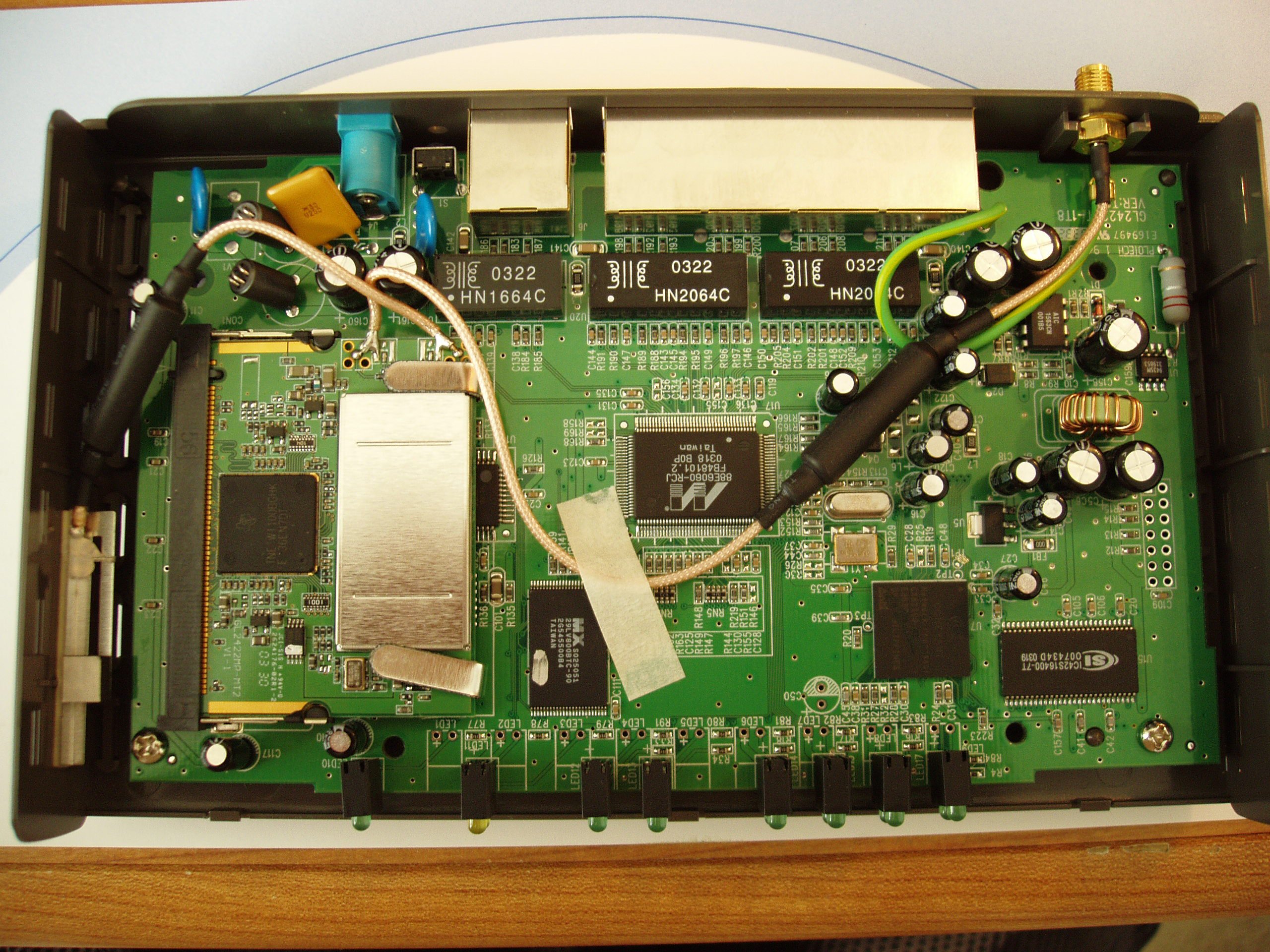
D-Link
DI-614+
Hacking / Reverse Engineering Page
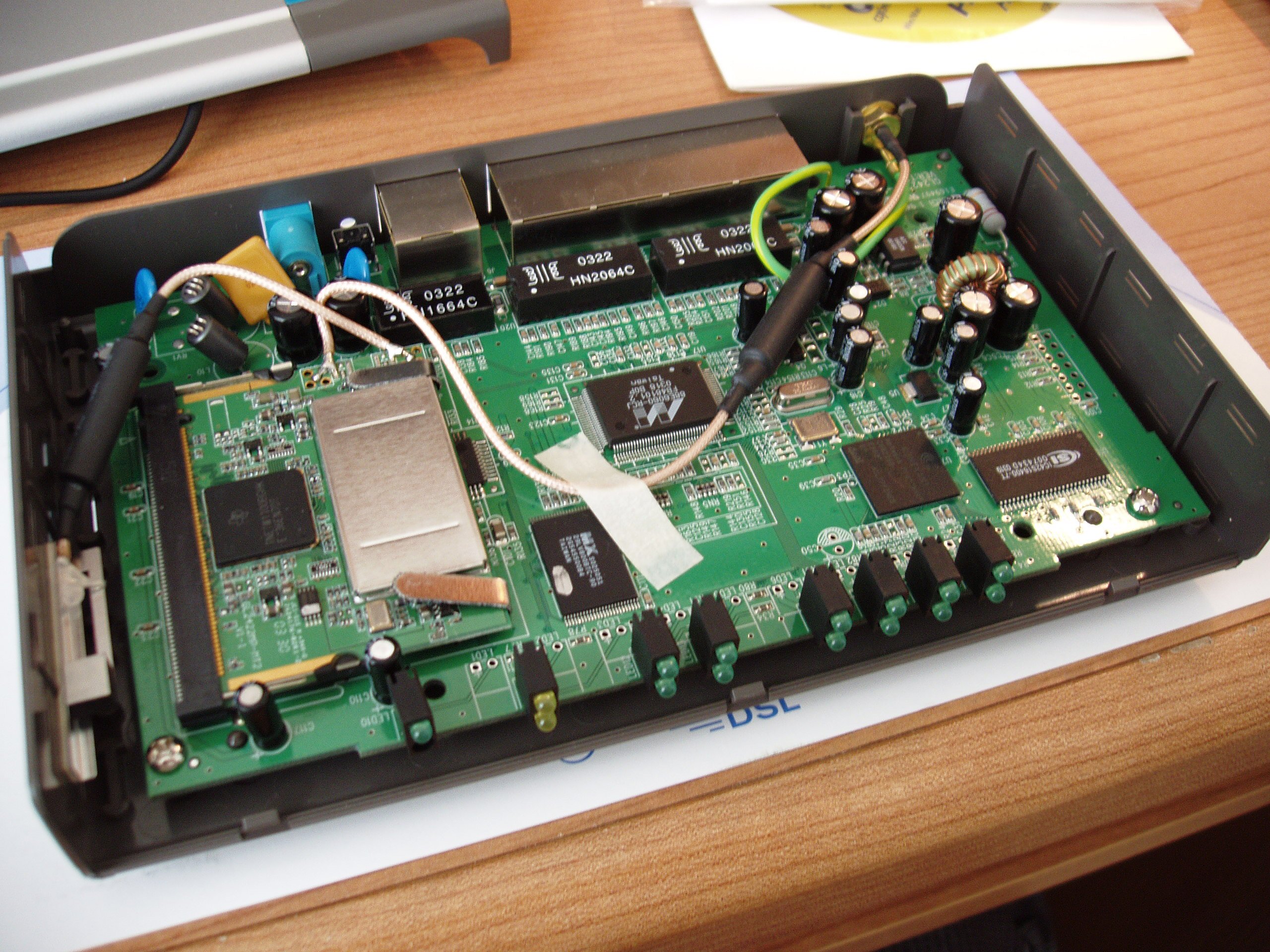
Very basic stuff, just playing with
hardware/firmware; don't expect to be inspired.
This is just a small site I put
together after taking apart my
[worthless] DI-614+ (now discontinued). This router is a piece of junk.
It still works, but it has to be reset almost everyday and it's
wireless signal strength is SUPER BAD. So one day I decided to take it
apart to see what I can do with it and how it looks inside and
here it is. This site is by no means the definitive location to get
info on the 614+, there are other (probably better sites). But this is
just my own little project. The main
goal of this is to get shell
access (from the current firmware
release) or even run Linux on the 614+ if at all possible. This
page was
started by me, for me, and with little to no research on the subject of
614+ hacking (which later turned out to be a pretty extensive topic,
mostly regurgitated info and no real-deal linux on 614+ info). If this
is new to you, enjoy, if you've seen this before, please feel free to
move on.
Note: This is Revision B. So
what you see here is for the LAST DI-614+ (discontinued).
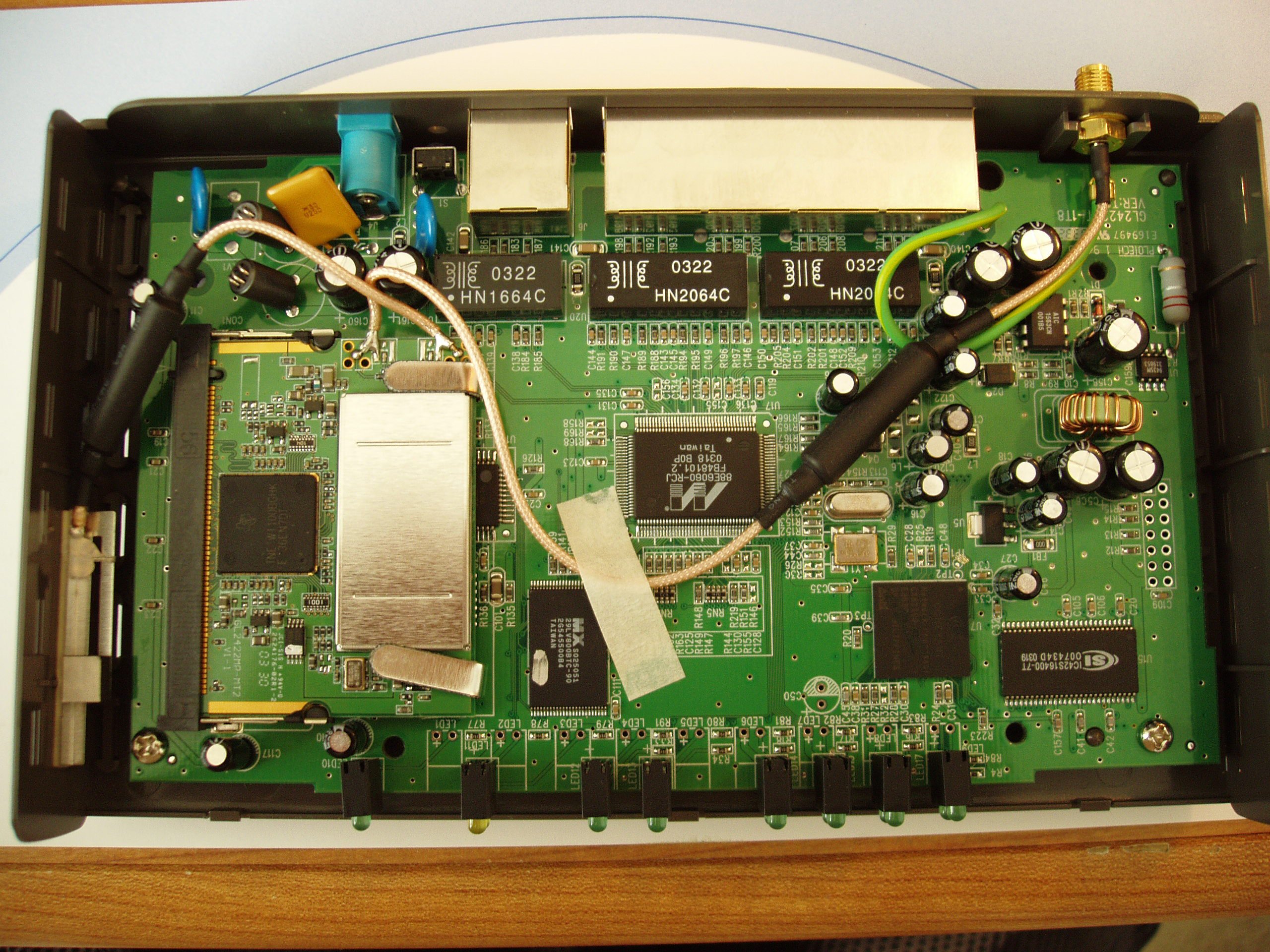
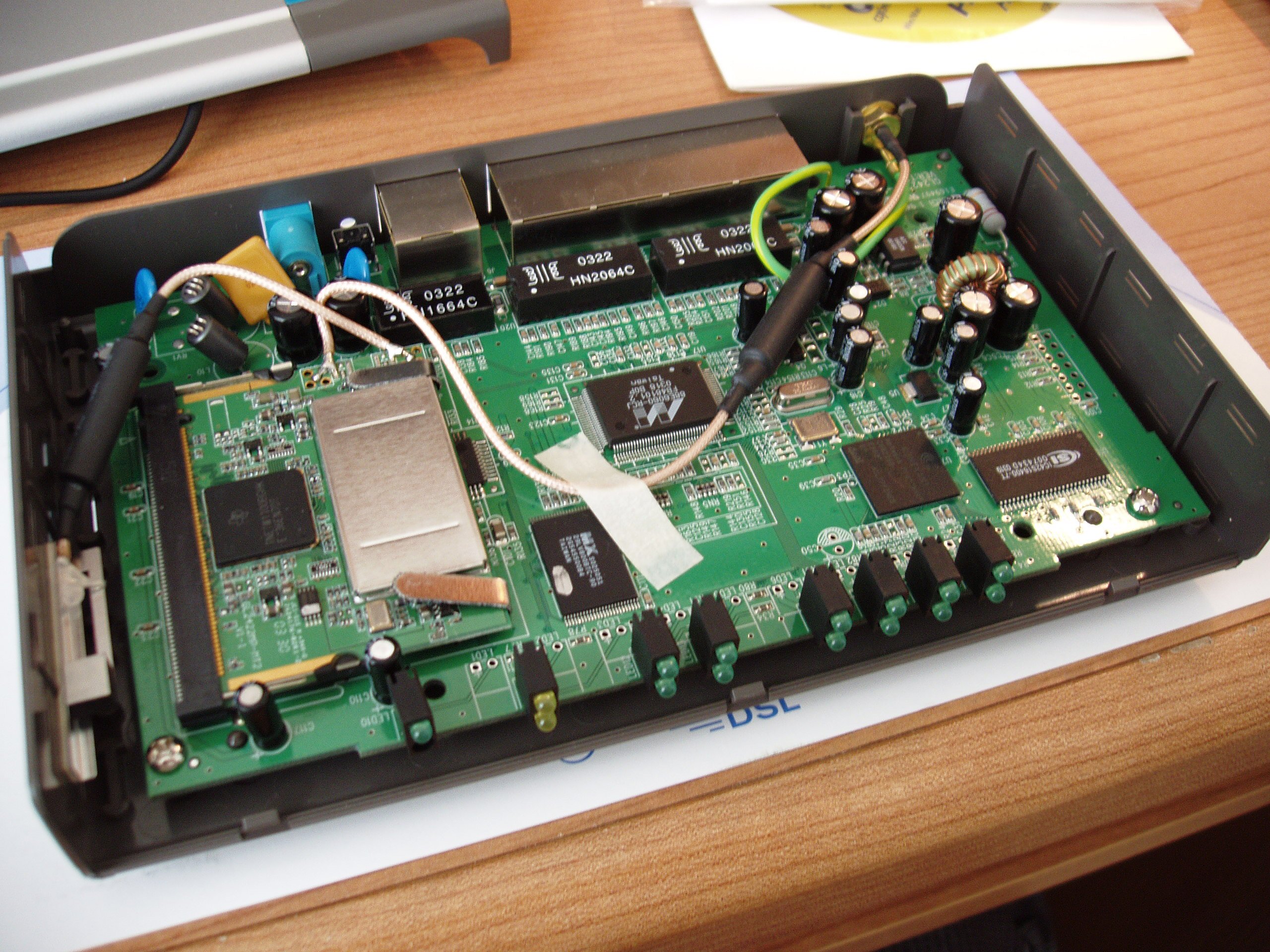
Click to view bigger image.
Click to view bigger image.
CPU Info:
Conexant
Network Processor
CX82100-41
E363335.1
0318 PHILIPPINES
ARM
Other Info:
OEM ID: GL2422RT-1T7
ARM9 Conexant CX82100-41 168Mhz
Global Sun Tech GL2422RT-1T8 v1.1
1MB FLASH (29LV800BTC-90)
8MB RAM (ICSI IC42S16400-7T)
Ethernet (Marvell 88E6060)
Wireless TI ACX100 mini-pci
There is a document online (
here)
that says that Revision A of the 614+ can be flashed with Firmwares
from TrendWare (TEW-311BRP), Eusso (GL2422-RT) and PheeNet (WBIG-104b+)
routers which all originate from Global SunTechnologies in Taiwan. It
also says there is currently no firmware for Revision B that can be
substituted into the 614+. The main point I was looking was for
confirmation that there is a telnet config mode, and
there is. Now I
guess it's my job to keep researching telnet config mode for RevB of
the 614+. There has to be a way to enable this mode. If not, I'm going
to CONSIDER flashing my 614+ with a firmware from one of those routers
but with updated ARM9 processors (
if
those even exist.)
Playing with the Firmware:
The firmware can be opened with WinRAR to
extract "Nml.mem" which seems to be the main FlashROM data for the
Connexant chip?? I'm still new at embedded stuff hacking. But looking
around inside the image file, there seems to be alot of cool stuff that
can be done with a little hex-editing! I'm so excited.
Now to figure out the file format of Nml.mem....extracting .GIF files
is pretty easy though, finding the start and end of the files is pretty
damn easy as they are stored one after the other (GIF89a - 0x47 0x49
0x46 0x38 0x39 0x61 signals the start of a GIF file and 0x00 0x3B seems
to signal the end if I recall). If you want to extract the files to
modify them just use a program that extracts file formats out of files
(I forgot the name of an old DOS program I had that did this..) Anyway
here is an example of a GIF file extracted straight from Nlm.mem (which
is inside the .bin):
Editing this while leaving the colors/size the same is very easy.
Stuffing it back into Nlm.mem is yet untested......TO DO.
UPDATE:
I managed to
extract all the GIF's and
JPEG's stored in the firmware image (22 GIFS, 100 JPEGS). Now to
extract the HTML and Executables stored in Nlm.mem.
Interesting strings
inside the Firmware:
1) Looking for all the
text-strings in "Nlm.mem" we find this:
WDB8WvbXdHtZyM8Ms2RENgHlacJghQyG
|
Previous
experience with software protections and just lots of reading tells me
that this looks like a hash. Could the password for the router
be computed against this hash? I dunno. I would like to know
though...Then to find a way to extract the encrypted hash out of the
router memory...ugh..never mind, whats the point?
Also inside that same file is this string: "dbgout.txt" I'd like to be
able to access this and see what it has.
2) And now for the most
useless stuff inside the Nlm.mem file:
Hey Moe, it dont woik. NYUK NYUK NYUK NYUK *bop* Owww!
|
YES, this was taken out of Nlm.mem! I have NO IDEA why it's
there (crazy programmers). Or when it shows (possibly through a console
error message).
3) Here is another interesting
string:
This is a strange problem.
|
YES, this was taken straight out of Nlm.mem. Heh, just had to put it up
here.
4) HELLO!!!%#@ Look what we
have here:
GST Telnet server v1.0
!!! idle timeout (5 minutes) !!!
TELNET: bind error
TELNET: open socket fail
TELNET: setsockopt SO_REUSEADDR error
|
A little further own down the file we see this:
Remote Managment Telnet Server
|
Looks like there IS a telnet server on this little sucker!!! I
HAVE TO FIGURE THIS OUT!!
5) Here is some more
interesting stuff, looks like the MiniPCI
card has a PRISM2 chipset (or
not?) and ACX100TSK (on the chip it
says AGX100AGHK) is the
Texas Instruments wireless network chip (there's a project to write
Linux drivers for the ACX100 chipset at http://acx100.sourceforge.net/
but I won't bother taking out the miniPCI card at this moment) Here
is the FCC-ID page that has a ton of info on the ACX100 card including
pictures HERE
(PDF file) and manual
here:
nInitializing Wireless Interface...OK !
Send WIRELESS_INIT_FAIL_TRAP
Initializing Wireless Interface...Failure !
Reinit WLAN driver (2) !
PRISM2_AP
Repeater disconnects with AP...
Start Easy backup mode.
802.11 Ad Hoc starts. BSSID = %02x:%02x:%02x:%02x:%02x:%02x
AP Client disconnects with AP.
Start Complex backup mode.
restore apclient timer
ACX100TSK
Michael error : Stop.
Check 22m rates
Repeater connects with AP. BSSID = %02x:%02x:%02x:%02x:%02x:%02x
AP Client connects with AP. BSSID = %02x:%02x:%02x:%02x:%02x:%02x
802.11 Ad Hoc connects with other. BSSID = %02x:%02x:%02x:%02x:%02x:%02x Channel:%d
AP is swapped by backup AP
Repeater disconnects with AP.
AP Client disconnects with AP.
Repeater disconnects with AP.
AP Client disconnects with AP.
ping complete
Memory Block Free Error!
Reinit WLAN driver (4) !
Reinit WLAN driver (5) !
Reinit WLAN driver (1) !
Reinit WLAN driver (3) !
.hteCPU did not start after boot from flash
Failed to download firmware to the ACX100
Timeout waiting for the ACX100 to complete Initialization
|
Here is some info gathered from the
FCC website about the miPCI card in MY DI-614+:
Prodect Name: Wireless 22Mbps Mini PCI
Card
Model Name: GL2422MP-MT FCC ID: KA2ACX100
6) Here we see that this
little sucker runs the ThreadX RTOS:
Copyright (c) 1996-2000 Express Logic Inc. * ThreadX ARM7/Green Hills Version G3.0f.3.0c
|
Ok the 614+ seems to run Express Logic's ThreadX Real-Time
Operating System (www.expresslogic.com)
on ARM's (www.arm.com) ARM9 (the RevB has an
ARM9, but this looks like it is backwards compatible with the ARM7
specs??)
processor from a little research it looks like Green Hills Software Inc
(www.ghs.com) licensed ThreadX from Express
Logic, or I could be wrong..
Final outlook: After looking
through Nlm.mem I am 100% sure there HAS to be a way
to enable DEBUG MODE/REMOTE TELNET SERVER. Whether it's possible by
some debugging/hex editing or
something, I
don't know. But there are just too many clues to have it any other way.
I wish I had an ARM debugger....
This page (http://www.dlink.pl/presse/artikel_detail.asp?docid=DLPI020902)
has a mention of "Web-based and Telnet configuration" on the 614+ I'd
like to know how to enable telnet configuration...
Links:
Page by roto - roto_at_mozy.org
12/2004